Browser Update Malicious Distribution Relies on Deceptive
Deceptive Browser Updates Exploit Rising Threat Activity:
A Closer Look In the ever-evolving landscape of cybersecurity threats, researchers from Proofpoint have recently identified a concerning trend in malicious activity that employs fake browser updates as a means to disseminate malware. This deceptive tactic, designed to lure unsuspecting users into downloading harmful software disguised as legitimate browser updates, has seen at least four distinct threat clusters in action.
The Art of Deception: Fake Browser Updates
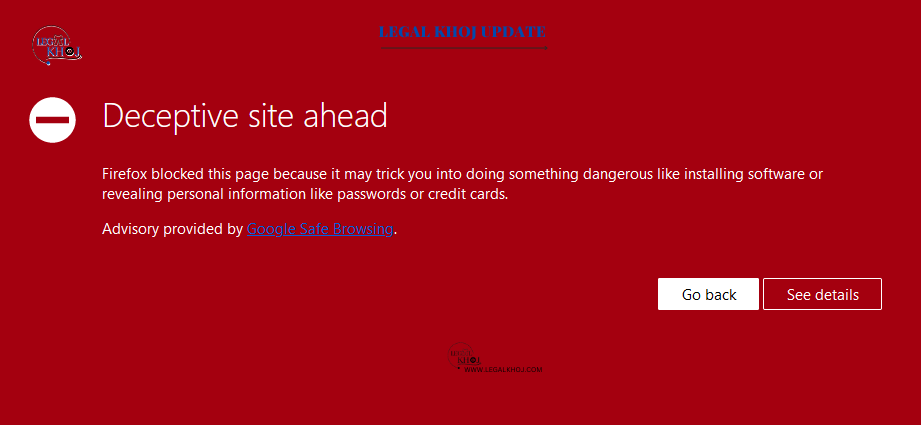
The term “fake browser updates” refers to compromised websites that display false notifications resembling updates from popular web browsers like Chrome, Firefox, or Edge. These fake notifications trick users into downloading malicious software, exploiting their trust in known and safe websites. This approach is especially insidious because it capitalizes on users’ belief in the legitimacy of the source, often bypassing security awareness training.
The Players: Threat Actors and Their Methods
Among these fake browser update threats, TA569 stands out as an established threat actor that has been using this technique for over five years to distribute the SocGholish malware. However, more recently, other threat actors have adopted this strategy, raising concerns in the cybersecurity community.
The threats at hand infiltrate websites by utilizing JavaScript or HTML-injected code to direct traffic to domains controlled by the threat actors, subsequently initiating the automatic download of malicious payloads. Each campaign employs unique techniques to filter traffic, making detection a challenging task.